TryHackMe - Developers"R"us
Writeup of the TryHackMe room Developers"R"us
Writeup of the TryHackMe room Developers"R"us
When importing a threat feed with a considerable amount of data in it, someone on the team forgot to set the expiry date. No expiry date = no expiry… For reasons I don’t understand, there’s no way to do mass deletion in the Azure Portal. So I had to resort to modifying my incident-closure-script in order to fix this blooper.
For reasons I had about 28k incidents I needed to close in Azure Sentinel, and the interface will only allow me to bulk close 50 at a time. What to do?
For December 2021 River Security hosted a Christmas CTF. This is my writeup for the challenge.

This blog post is a review/summary of my experience with the Burp Suite Certified Practitioner exam. All of the information on this page are publicly available on the PortSwigger website. This review/summary does not contain any spoilers. PortSwigger has this to say about this training path: By becoming a Burp Suite Certified Practitioner, you will be able to demonstrate your web security testing knowledge and Burp Suite skills to the world....
Slack (and other Electron apps) often use cookies to store session/access tokens. Perhaps we can extract and use these tokens for phishing awareness training?
Use CSS and HTML to hide and replace administrator injected alerts in Office 365

I’ve had my eyes in the AWAE course for several months, and initially thought it would be too difficult for me to do this year. But then I just decided to give it a try! Note: This blog post is very low quality compared to the one I wrote about My OSCP experience, I encourage you to go read An experience leading up to Offensive Security Web Expert by loca1gh0s7, which was my inspiration for starting on this journey....
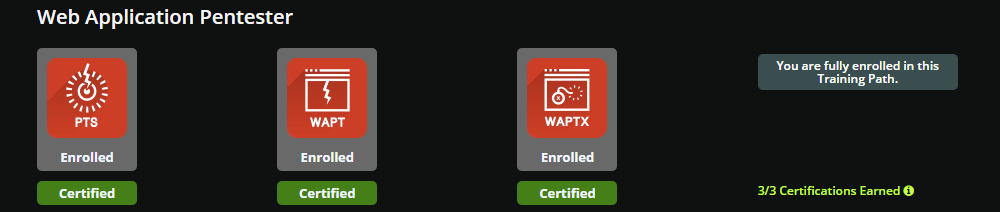
This blog post is a review/summary of my experience with the eLearnSecurity Web Application Pentester training path. eLearnSecurity has this to say about this training path: The Web Application Pentester path is the most advanced and hands-on training path on web application penetration testing in the market. This training path starts by teaching you the fundamentals of networking and penetration testing, then proceeds to providing you with the established web application penetration testing methodology and the latest web attacks, and ultimately showcases how to execute more advanced and complicated attacks, by heavily manipulating web application components....

After I started looking at OSCP, I also noticed OSWP - which seemed like a much shorter, and simpler, course. I knew it was old, but it was still interesting enough that I wanted to give it a go. My advice Pre-WiFu advice Make sure to purchase the correct equipment. I recommend sticking to the recommended hardware (see what I used further down). WiFu advice Read all of the PDF, even the highly technical boring stuff Take notes (I recommend Markdown in VS Code) Do the exercises and write down your steps (good training for the exam report, and nice to have later) Use the latest Kali, or whatever Linux distro you prefer (no need to use the provided image) Exam advice Schedule your exam a couple days in advance Schedule the exam for a time slot that best fits you Use the provided report template Keep it simple Take notes and screenshots My background I’ve been a hobby coder since I was 10, and a professional developer for a long time, so I know my way around a computer....